HMAC
Computation and verification of a Hash-based Message Authentication Code (HMAC). Sometimes known as Keyed Message Authentication Code or Keyed hash, HMAC uses a cryptographic hash function like SHA-1, SHA-224, SHA-256, SHA-384, SHA-512, or MD-5, applied to a "message," along with a secret key, to produce a signature or message authentication code on that message.
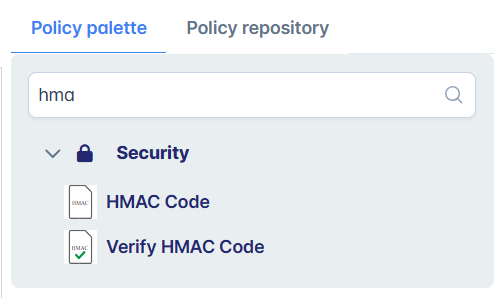
Policies under this category are:
